First introduced in 2012 by a consortium of industry leaders, Domain-based Message Authentication, Reporting and Conformance (DMARC) is an open standard authentication protocol that works with SPF and DKIM to prevent the fraudulent use of legitimate brands in email attacks. More than 2.5 billion mailboxes are DMARC-enabled worldwide.
At its most essential, DMARC enables email receiver systems to recognize when an email isn’t coming from a specific brand’s approved senders and gives the brand the ability to tell receivers systems what to do with these unauthorized emails.
In summary, DMARC validation is an email standard that:
- confirms the sender’s identity using Sender Policy Framework (SPF) and DomainKeys Identified Mail (DKIM)
- tells the recipient’s email service what to do with emails that fail the check
- asks recipient email services to provide reports of where email comes from
The receiving email service uses SPF and DKIM to confirm the sender’s identity. If the receiving email service confirms the sender’s identity it will forward the email to the receiver’s inbox. If the receiving email service cannot confirm the sender’s identity it will mark the email as spam.
Benefits of DMARC
By using DMARC, you can:
- help protect your users, employees, and reputation from cybercrime
- reduce customer support costs relating to email fraud
- improve trust in the emails your organization sends
- see the legitimate and fraudulent use of your domains via DMARC reports
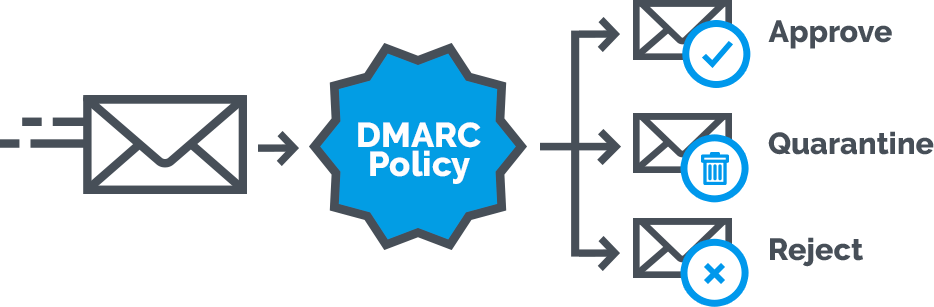
What is a DMARC Enforcement Policy?
The idea behind setting up a DMARC enforcement policy for your organization is to instruct email receiving systems what to do when email purporting to come from your approved domains fails authentication. Such policies include:
- p=none: Email is delivered to its intended recipient without restriction
- p=quarantine: Email that fails authentication is sent to the intended recipient’s junk folder
- p=reject: Email that fails authentication gets deleted and never reaches its intended recipient
The Mechanics of DMARC
DMARC uses DNS as the mechanism for policy publication. DMARC records are hosted as TXT DNS records in a DMARC specific namespace, which is created by prepending “_dmarc” to the email domain.
For example, if the email domain “example.com” publishes a DMARC record, issuing a DNS query for the TXT record at “_dmarc.example.com,” will retrieve the DMARC record.
Email receiver systems use the policies published to inform how they process emails purporting to come from the sender’s email domain.
Setting up DMARC for your DNS
Prior to setting up DMARC, ensure that you have SPF and DKIM deployed and authenticating messages. Once done follow the below steps to add DMARC to your DNS.
Step 1: Create a DMARC Record
- Use Agari’s DMARC Setup Tool to easily create the required TXT record. It should look something like this:
v=DMARC1; p=quarantine; pct=100; rua=mailto:dmarc@yourdomain.com
This example record instructs receiver systems to generate and send aggregate feedback to “dmarc-feedback@” your domain. The p=none tag indicates you are only interested in collecting feedback. Alternatively, you could use a p=quarantine, or p=reject tags for emails that fail authentication.
This tells anyone receiving email from you that:
- You have a DMARC policy (
v=DMARC1) - Any messages that fail DMARC checks should be treated as spam (
p=quarantine) - They should treat 100% of your messages this way (
pct=100) - They should send reports of email received back to you (
rua=mailto:dmarc@yourdomain.com)
Step 2: In your DNS, follow these DMARC setup steps to create a DNS TXT record.
- Log into the management console of your DNS hosting provider, and while this can vary by provider, you want to locate the page that allows you to add a DNS TXT record
Step 3: In the Type box, select TXT Record Type
Step 4: In the Host Value box, enter _dmarc as the “host”
Step 5: In the TXT Value box, enter the record you created using the DMARC Record Creator
Step 6: Save the DMARC record
Step 7: Validate the DMARC setup
Taking DMARC to Scale
Setting up DMARC in DNS only takes a few minutes. But to be effective against brand impersonation, DMARC must be set to its highest enforcement level, p=reject. And while this is relatively straightforward when you’re talking about a single domain, it can be complicated and time consuming for organizations with thousands of domains spanning dozens of email senders and outside email distribution partners.
Why is DMARC is crucial:
studies from dmarc analyser reveals the following:
- $1.6 million on average is what one single spear phishing attack costs for organizations
- From 2013 to 2016 companies saw losses approaching $1.6 billion
- $500 million every year is scammed by phishing attacks
- Dealing with phishing attacks costs an average 10,000-employee company $3.7 million a year
- The average employee wastes 4.16 hours a year on phishing scams
- Between January 2015 and December 2016 dollar figures climbed sharply up with 2370% by phishing attacks
- Just 3% of all users will report phishing email to their management
- More than 400 businesses are targeted by BEC scams every day
- 76% of organizations have reported that they have been victim of a phishing attack in 2016
- Organizations that have reported being victim of a phishing attack in 2016: 76%
- 1 in 3 companies have been victims of CEO fraud emails
- 70% of all global emails is malicious
- The volume of spam emails increased 4x in 2016
- Q3 2016 the amount of phishing emails with ransomware has grown to 97.25% compared to 92% in Q1 2016
- 9 out of 10 phishing emails has some form of ransomware in March 2016
- Fake invoice messages are the #1 type of phishing lure
- The number of reported W-2 phishing emails in 2017 increased by 870%
- 78% of people claim to be aware of the risks of unknown links in emails. And yet they click anyway
- In the year 2016 over 400,000 phishing sites have been observed each month on average
- 30 percent of phishing emails get opened
- In 2016 1 out of 131 emails contained some form of malware, the highest rate in 5 years
Conclusion
You can use DMARC to protect your domains against abuse in phishing or spoofing attacks. As a website owner, you want to know for sure that your visitors or customers will only see emails sent from your organization. Therefore, DMARC is a must for every domain owner. Securing your email with DMARC gives email receivers certainty whether an email is legit and has originated from you. This results in a positive impact on email delivery and also prevents others from sending email using your domain.





